The 2024 Change Healthcare ransomware attack paralyzed billing capabilities for thousands of healthcare practices across the nation, and nearly 193 million American's health records were stolen from them as well as many practices experienced delayed claim processing and lost their ability to generate revenue. This event was a wake or break moment for many healthcare providers and made it clear that the security breach of your billing vendor is the potential financial disaster for you.
The reason for this increased concern is because HHS is proposing to make multi-factor authentication and encryption required for all electronic Protected Health Information (ePHI) through updates to the upcoming HIPAA Security Rule. In other words, no longer will simply stating that your billing vendor is "HIPAA compliant" be sufficient; rather, the practice will be subject to fines for failing to review the security protocols of its business associates.
Therefore, with the new changes, practices have options available to them. They can continue to outsource their revenue cycle services, however they need to do so by choosing vendors who have both demonstrated and been validated by a third party to utilize effective cybersecurity measures to protect patient data.
The 2026 Regulatory Shift: From Trust to Verification
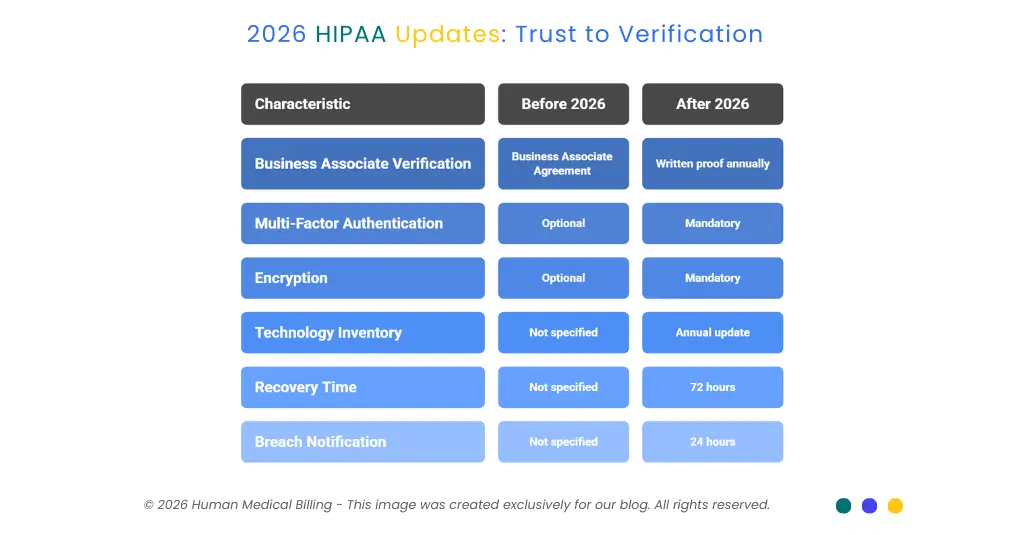
For more than 20 years, the HIPAA Security Rule has given health care providers the option of implementing certain protections (referred to as "addressable") in a way they see fit. Those options are going away. In order to be compliant with the 2026 HIPAA updates, the practice must get written proof from their business associate(s) every year at minimum which verifies that the technical safeguard requirements have been met.
A Business Associate Agreement will no longer be enough to prove this requirement has been met.
The practice needs to understand the following regarding the new environment.
1. Mandatory Multi-Factor Authentication
Multi-factor authentication will be mandatory for every method of accessing the computer system as part of the new Security Rule, (not just remote) and, your billing services provider must implement multi-factor authentication across every user who has access to your patient's information.
2. End-to-End Encryption Requirements
Encryption is no longer optional. The proposed rule makes encryption a required safeguard. Encryption at rest is now mandatory and must meet or exceed current NIST Cybersecurity Standards for Secure Key management and access controls. As such, your billing partner must have encryption for data that is traveling between systems and must also encrypt data that resides in their database(s).
3. Technology Asset Inventory and Network Mapping
A healthcare organization is required to create and update its technology asset inventory and a network diagram illustrating the electronic protected health information (ePHI) flow at least once each year for the last 12 months. The healthcare organization wants to know if their healthcare revenue cycle management service provider will be able to clearly identify all locations and paths that ePHI is transferred throughout their systems.
4. 72-Hour Recovery Requirement
Contingency planning standards were updated so that organizations must have demonstrated the capacity to recover critical systems within 72 hours of occurrence after an incident. HHS has emphasized the importance of restoring operations quickly as a key component of a strong security program with ransomware guidance issued by the department. If a ransomware event occurs at your billing company, will they be able to process your claims within 3 days?
5. 24-Hour Breach Notification from Business Associates
New verification standards are being applied to business associates under this proposed regulation regarding compliance with applicable safeguards and contingency plans within 24 hours of activation. Will your billing partner contact you within 24 hours of identifying a security breach?
Why "HIPAA Compliant" Badges Are Red Flags in 2026
If you look at any medical billing provider's website you'll find HIPAA compliant logos plastered all over the place. The problem is that HIPAA compliance isn't something that can be certified by just anybody. HIPAA compliance is an enforceable law that can only be confirmed with demonstrated policies, procedures and controls.
Medical billers experienced the most expensive year for breaches in history in 2024 as the median breach costs reached $7.42 million. These were many times caused by business associate vendors that had poor security posture.
There was a 30% increase in ransomware attacks against medical billing vendors in 2025 versus 2024. In addition to hospital systems, cyber criminals have been focusing on third party vendors because they often have fewer protections than the hospitals, yet provide access to large amounts of sensitive information about patients.
Conclusion: Being self proclaimed compliant is worth zero dollars. Being validated by a third party is worth millions.
HITRUST r2 and SOC 2 Type II: The Gold Standard for RCM Security
Smart practices now require their medical billing services partners to have independently verified certifications. Two stand out from the rest:
1. HITRUST r2 Certification
Hitrust consolidates all of the requirements from authoritive sources including ISO, NIST, HIPAA and PCI DSS into a single, integrated set of controls A-LIGN. This means that a billing company with HITRUST certification has undergone third party audits against dozens of security frameworks at once.
In 2024, environments maintained by HITRUST certified companies reported a breach-free rate of 99.41%. These are not self-assessment results. HITRUST requires rigorous, third-party validation that is adaptable to evolving threats.
The HITRUST r2 assessment evaluates security controls against a broad range of authoritative sources using a scalable, risk-based methodology and represents the highest level of assurance. For revenue cycle management vendors handling millions of patient records, this type of scrutiny is essential.
2. SOC 2 Type II Certification
While HITRUST focuses on information security for the healthcare industry; a SOC 2 Type 2 audit assesses whether a provider of services maintains effective security controls for a long duration (usually 6-12 months).
The SOC 2 Type 2 audit assesses a vendor across 5 trust service criteria: availability, processing integrity, security, confidentiality and privacy. These criteria are directly relevant to the operational risk exposures practices have when providing denial management services and medical accounts receivable services.
A key distinction between a point in time assessment and a SOC 2 Type 2 audit is that the SOC 2 Type 2 audit verifies whether the security controls operate consistently and as intended during the normal course of business. Since your billing partner is continuously processing claims, this is a critical consideration.
Your RCM Vendor Audit Checklist
Practicing smart business administrators are being more stringent in the due diligence process prior to signing billing agreements with companies. The use of this checklist can be helpful in determining if an organization is a suitable candidate as a business partner:
1. Demand Proof of Independent Certification
Request the full (not a summary) SOC 2 Type II or HITRUST r2 compliance audit reports from the company you are considering. All vendors of quality should be able to provide this documentation confidentially under a non-disclosure agreement (NDA). If they refuse to provide the documentation, do not consider the company as a viable candidate.
2. Verify Annual Penetration Testing
The organization performing the HIPAA Security Risk Analysis should verify its security controls annually through penetration testing using qualified security experts. Request information on when the most recent penetration testing was completed and by whom it was performed.
3. Check Patch Management and Vulnerability Scanning
How rapidly does your potential partner respond to apply patches for critical vulnerabilities? Does the company continuously scan for new vulnerabilities? In 2025 ransomware attacks reached the highest levels in history increasing by 58% from 2024, largely because many organizations were attacked by exploiting vulnerabilities that had been known for months or years and should have already been patched.
4. Confirm Disaster Recovery Capabilities
Can the company you are considering restore operations within 72 hours? Documented recovery time objectives and recovery point objectives are essential. Asking when the most recent disaster recovery plan testing took place is also beneficial.
5. Review Incident Response Procedures
Do they have a document that outlines how they will respond if a breach is detected? If so, will they be able to provide you with notice of a breach or unauthorized access within 24 hours of discovery as required by recent federal regulations?
6. Validate Encryption Standards
Are all patient records (at-rest and in-transit) protected using encryption? What are their encryption standards? Are their encryption keys properly maintained under NIST guidelines?
7. Assess Staff Training Programs
A phishing attack is currently the most common way for hackers to gain access to sensitive information for healthcare organizations and accounts for 16% of all reported healthcare data breaches through September 2025. Does your billing vendor regularly educate its staff on security awareness? Does your billing vendor conduct simulated phishing attacks to test employee compliance and/or vulnerabilities?
The Real Cost of Choosing Wrong
Using only price as a decision point when it comes to shopping for vendors is an enormous and devastating mistake. The total cost of ransomware downtime has already surpassed $21.9 billion in 2024. This number does not account for other costs such as regulatory penalties, customer notification, credit monitoring, and reputational damage.
In 2025, OCR issued more than $6.6 million in fines for HIPAA violations; the range of those fines was $80,000 to $3,000,000. In many cases, these penalties were based on inadequate risk assessments by practices and their lack of effective technical controls for their business associates.
Human Medical Billing understands that our comprehensive medical credentialing services and our medical coding services represent the starting point, but also know that we must have a strong foundation of security infrastructure to protect your financial interests, your reputation, and the trust of your patients. We will continually work to meet and maintain standards that ensure compliance and verification of all of our security measures so you may continue to provide the best possible patient care while we manage the complexities of accurate billing and protecting your valuable and sensitive patient information.

Contact Human Medical Billing to schedule a compliance readiness review or learn more about our end-to-end billing and regulatory support services.

